last updated: march 21, 2025
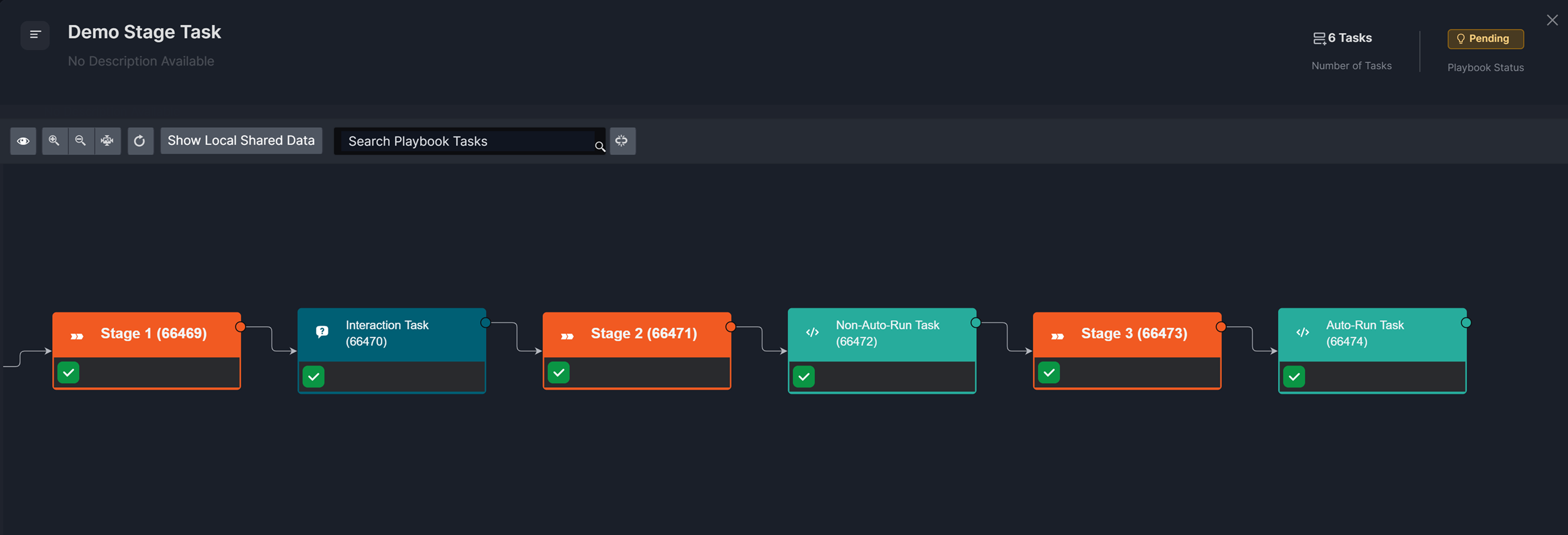
A stage task begins a phase where all tasks up to the next stage or leaf node form a unit of investigation—updated in the incident workspace. It marks transition points, reducing the need to sift through multiple tasks when tracing playbook execution or editing workflow.
-20250221-185822.png?cb=7578c5139af27a585b072ec210e681e4)
Stage Examples by Playbook Type
Example 1
A phishing playbook may include stages such as:
-
Email Analysis
-
IP Enrichment
-
URL Enrichment
-
Attachment Enrichment
-
Domain Enrichment
-
Threat Summary
-
User Notification
Example 2
An insider threat investigation playbook may include stages such as:
-
Anomaly Detection
-
User Behavior Analysis
-
Data Exfiltration Analysis
-
Identity and Access Review
-
Threat Correlation and Risk Assessment
-
Incident Escalation and Stakeholder Notification
Example 3
A cloud security breach response playbook may include stages such as:
-
Unauthorized Activity Detection
-
Asset Inventory and Exposure Assessment
-
Threat Intelligence Correlation
-
Containment and Access Restriction
-
Data Exfiltration and Integrity Check
-
Forensic Investigation and Log Analysis
-
Recovery and System Restoration
-
System Reinforcement
Stage tasks in branching workflows (2.1–2.4 in the diagram below) ensure clear organization and structured tracking, reducing task overlook and enabling efficient playbook management and communication across teams.
-20250305-211225.png?cb=fa38e5347782431d0661e810ca09314a)
Example - Tracking the Investigation Stage
Objective
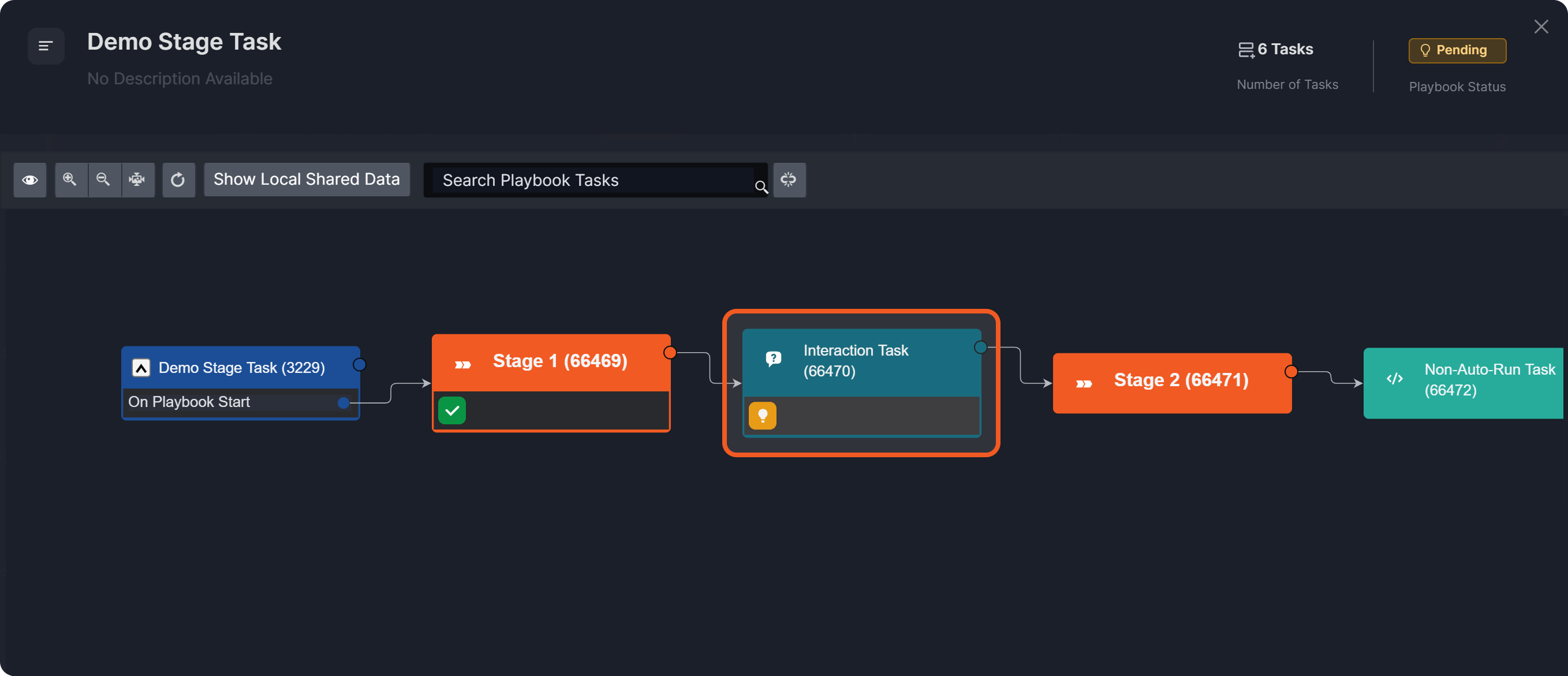
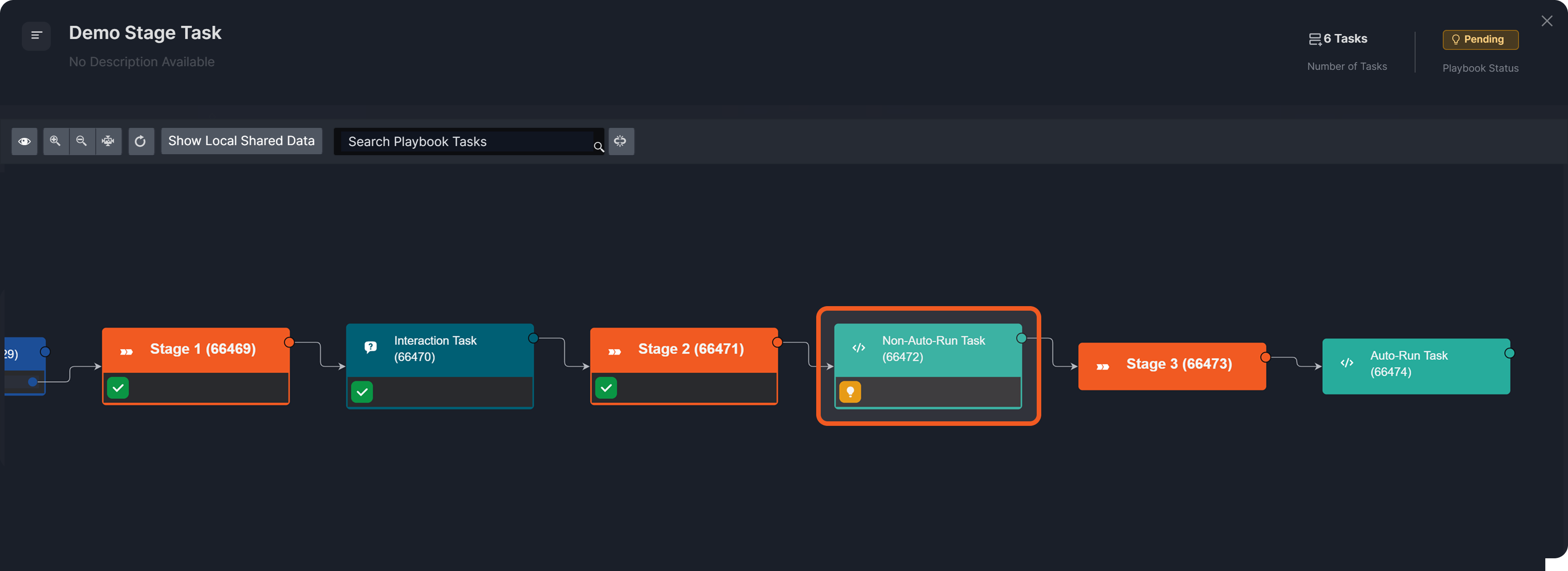
Tracking the execution of a live multi-stage playbook in the incident workspace as stages progress and complete.
-
Build the following playbook.
%201.png?cb=75b63bfc59371db5b2a876dd9e55c58d)
READER NOTE *
-
Ensure all stage tasks are configured to auto-run.
%201-20250303-220055.png?cb=cab6e709edb58d0d15bb4e54ef659eef)
-
Configure the first data formatter task as non-auto-run.
%201-20250303-220109.png?cb=ab9e9b3788edad90c6645669157c6180)
-
Configure the second data formatter task to auto-run.
%201-20250303-220055.png?cb=cab6e709edb58d0d15bb4e54ef659eef)
-
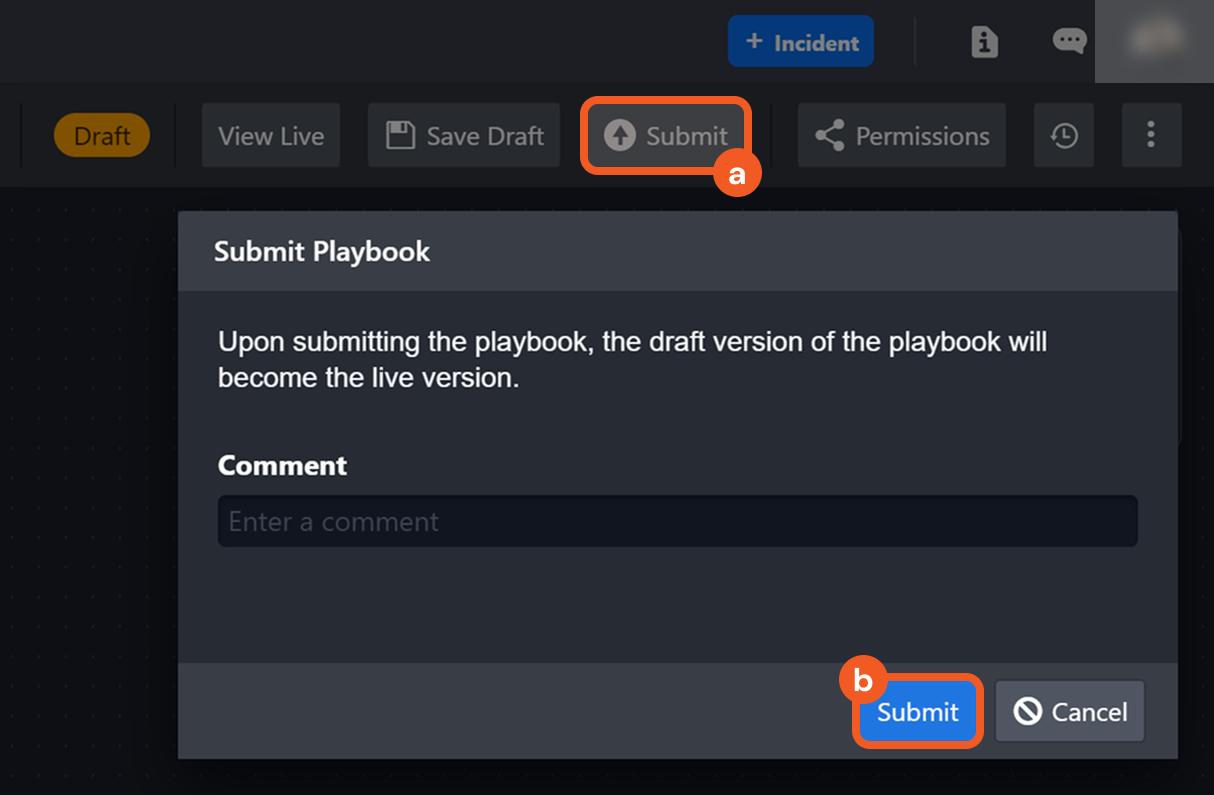
Submit this playbook.
-
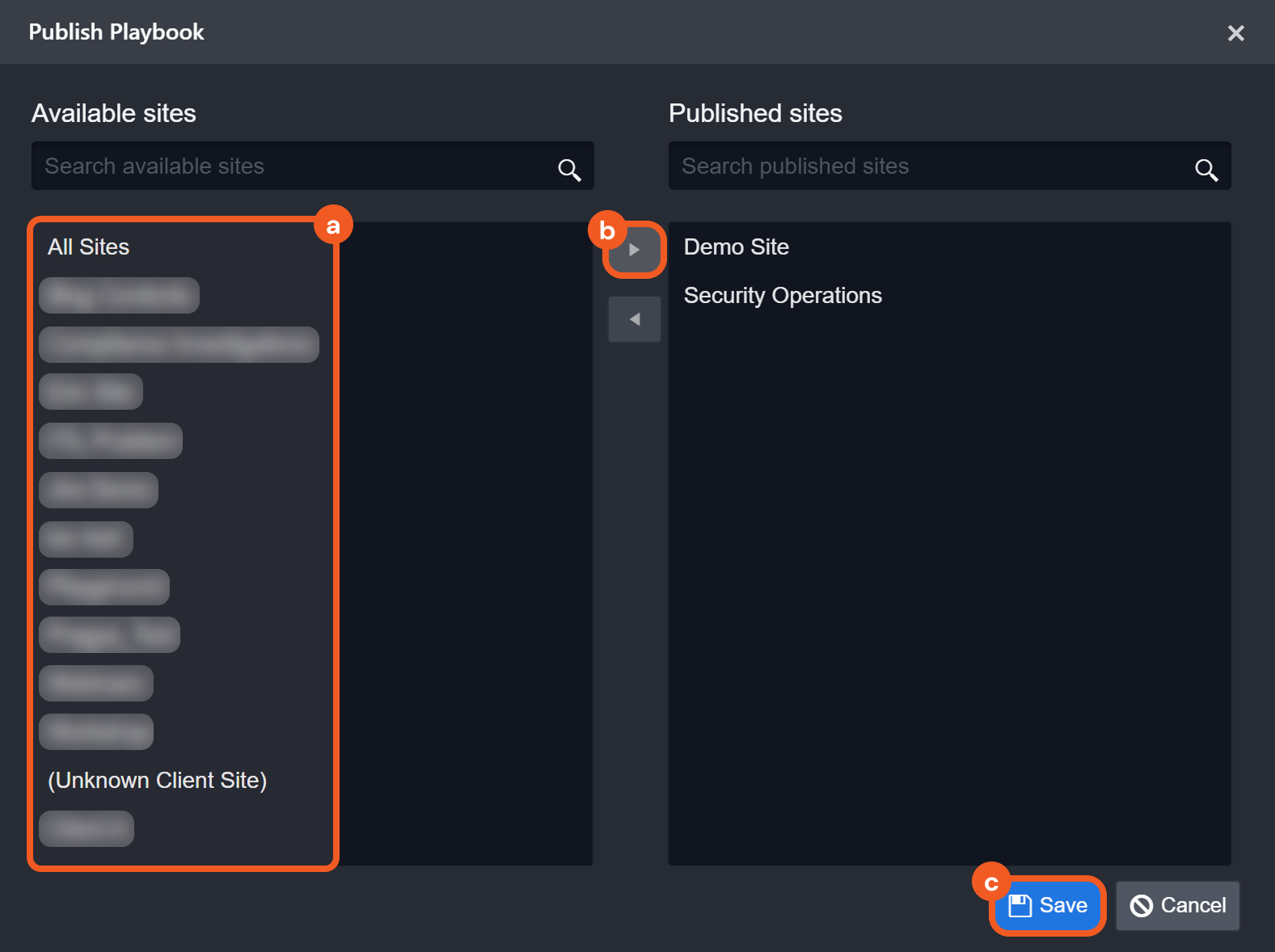
Publish this playbook to the relevant sites.
-
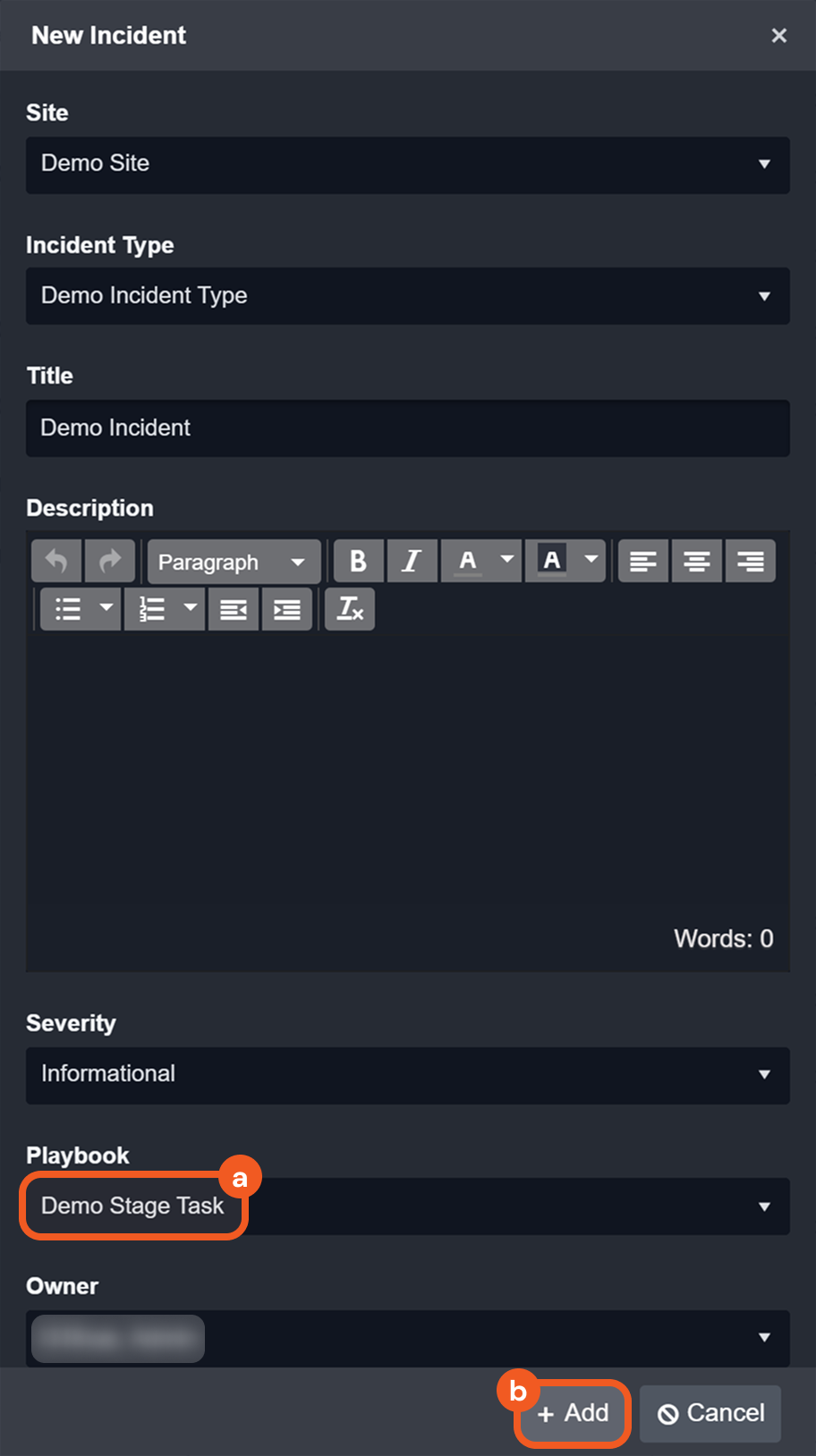
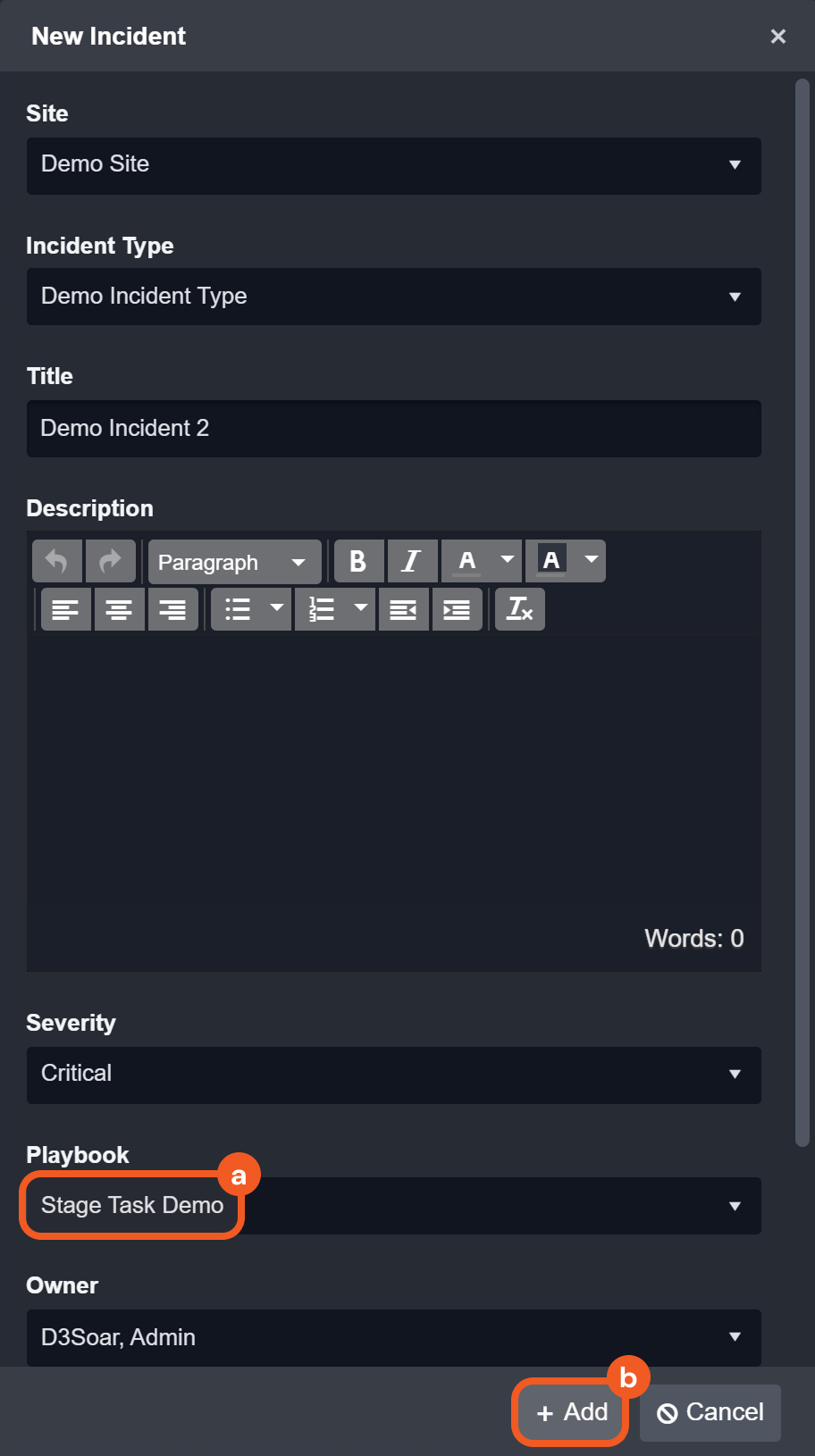
Create a new incident.
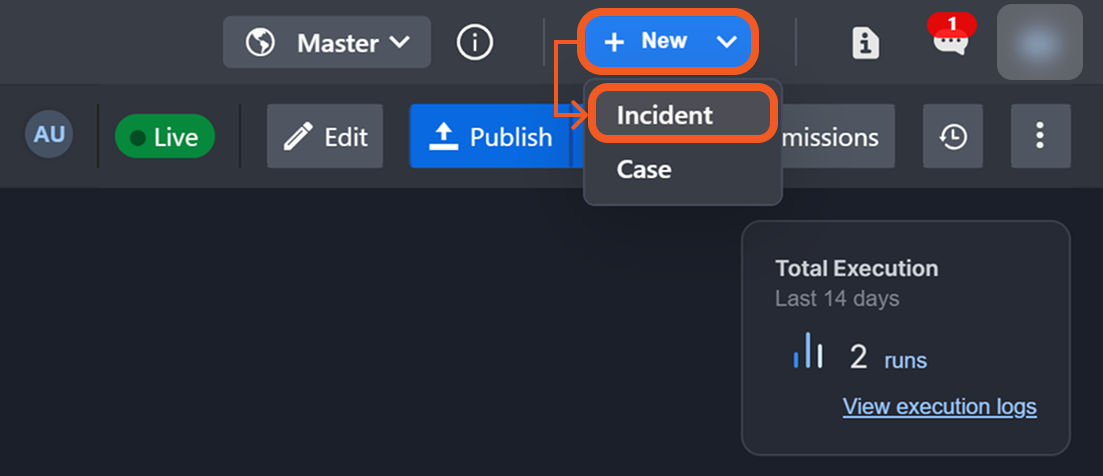
-
Configure the incident to run the submitted playbook, then click on the + Add button.
%201.png?cb=bed09c8b4ccdbac55e376929b1ea5427)
-
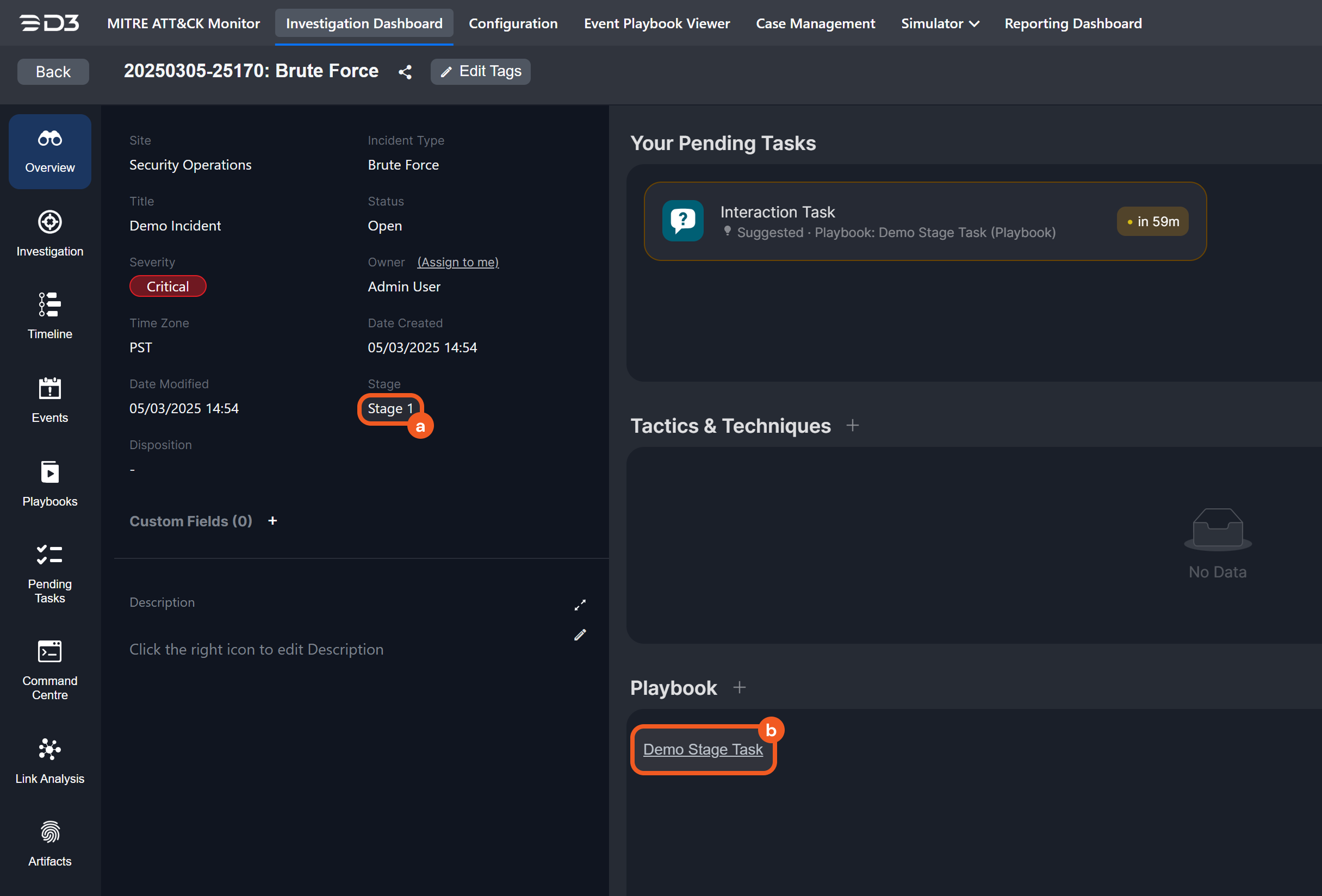
Navigate to the incident workspace of the manually created incident.
-
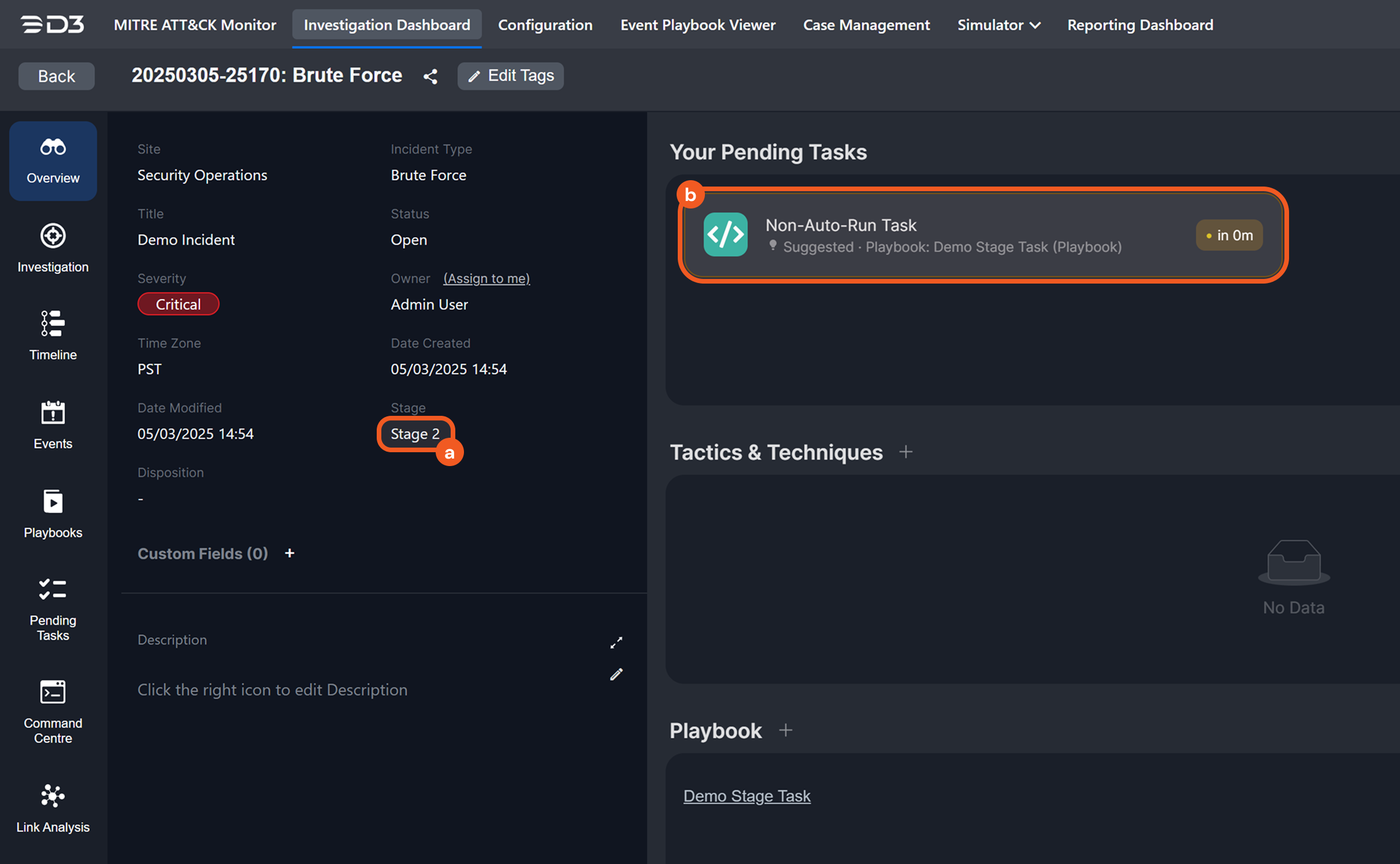
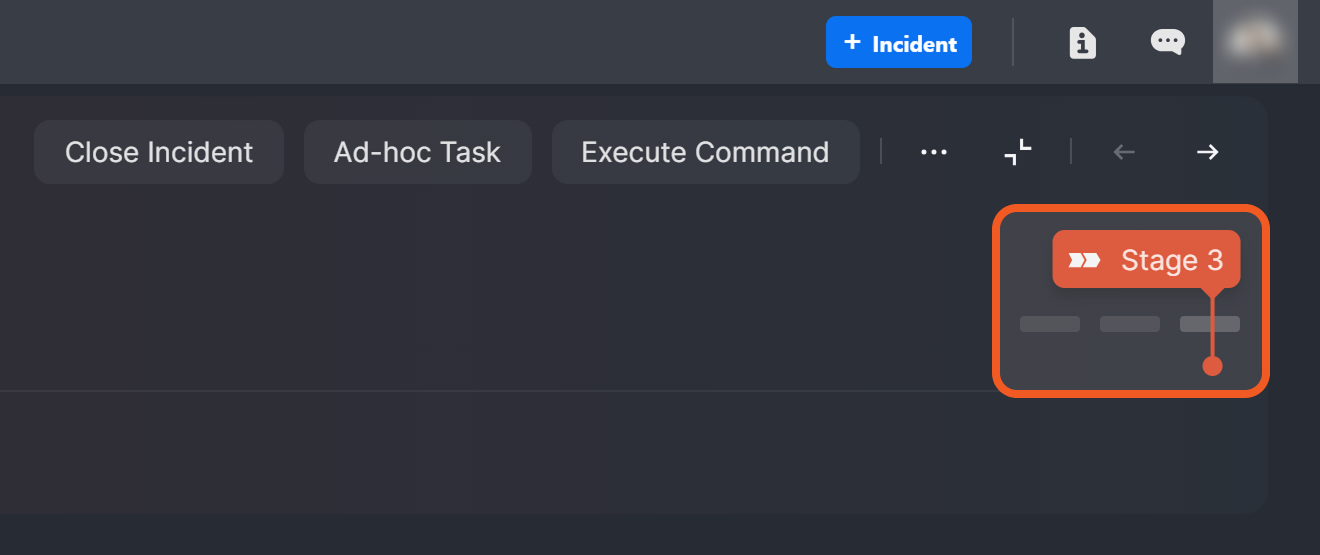
Observe the current investigation stage of this incident, then open the running playbook.
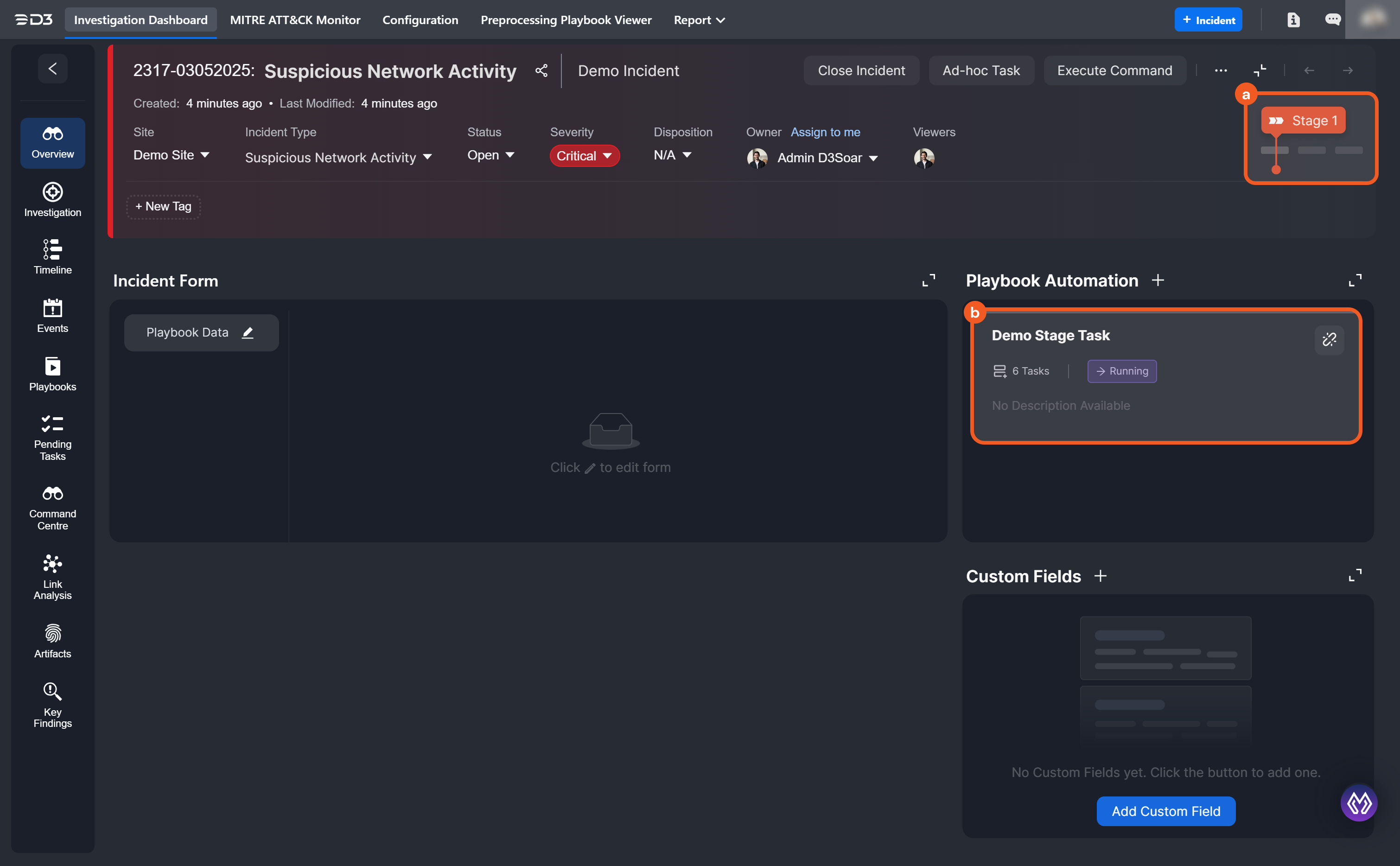
Incident Workspace UI in Earlier D3 Versions
-
Click on the pending interaction task.
-
Provide an input, then click on the 10.2.0.134_BetaPreview_VSOC_LifeServer.aspx_div=dashboard&Open=Other&t2=08b859c192aa477b646ed6674d44ec4fc61cc62429bafabfde553a46b91faa0a (13) 1-20250305-230558.png button.
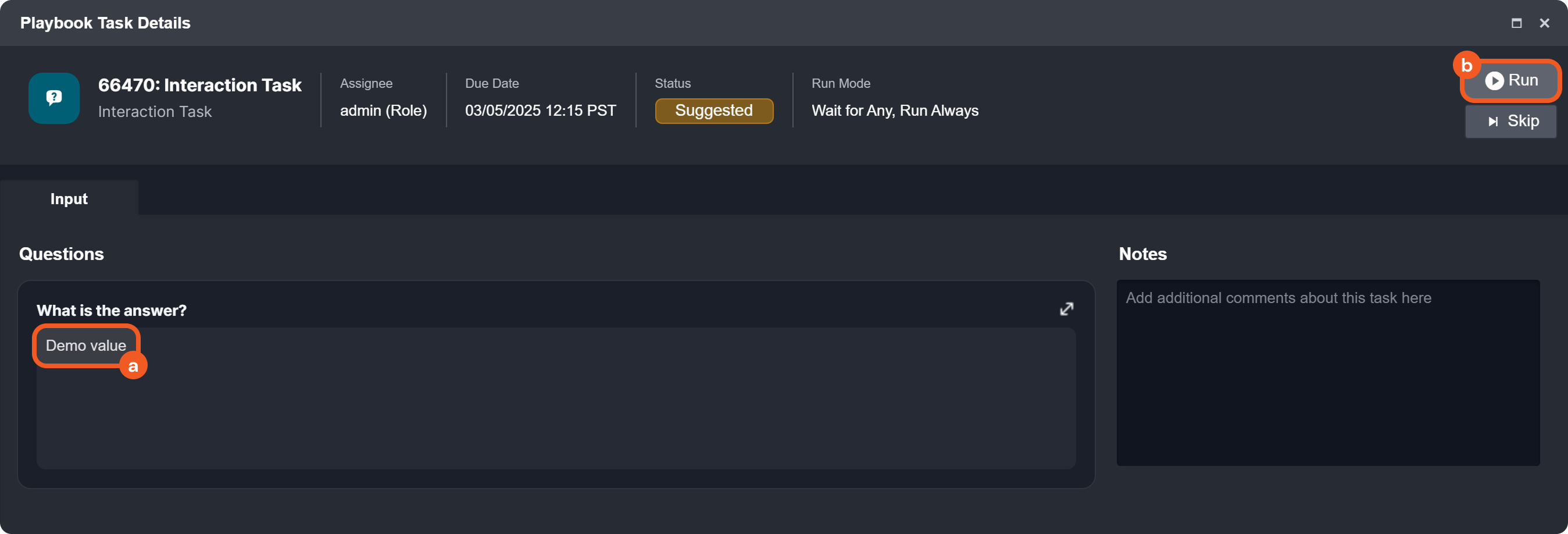
-
Observe the change in investigation stage, then return to the running playbook.
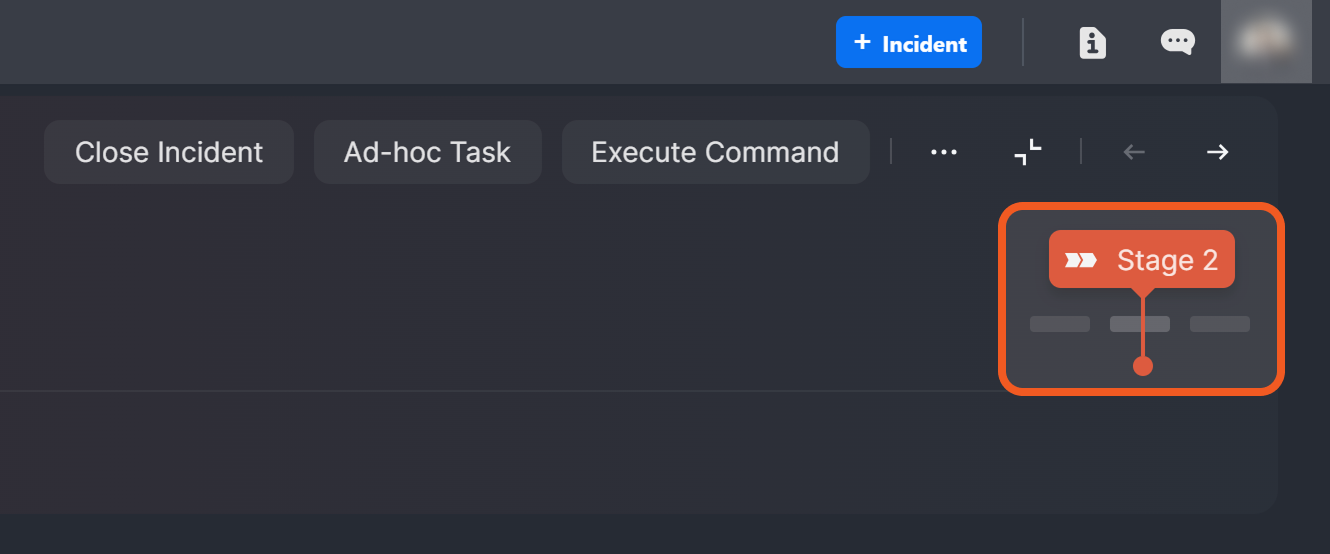
Incident Workspace UI in Earlier D3 vSOC Versions
-
Click on the pending data formatter task.
-
Click on the 10.2.0.134_BetaPreview_VSOC_LifeServer.aspx_div=dashboard&Open=Other&t2=08b859c192aa477b646ed6674d44ec4fc61cc62429bafabfde553a46b91faa0a (13) 1-20250305-230558.png button.
-20250305-231919.png?cb=54e930733e9860cc74e0fac2ba2db922)
-
Verify that all tasks have run to completion.
-
Observe the change in investigation stage.
Incident Workspace UI in Earlier D3 vSOC Versions
-20250305-232754.png?cb=d7a0255c17171cd838489748095d60ec)
Assigning Investigation Units
.png?cb=828a3d9a61364a1a6e557e62ba0346f1)
Non-auto-run stage tasks can be configured to require an assignee to initiate the corresponding investigation unit, with assignment based on username, role, or group. A due time may also be set to ensure compliance with SLA or business requirements.
In %201-20250311-025826.png?cb=80befef8fd74901408e92095987e4e74)
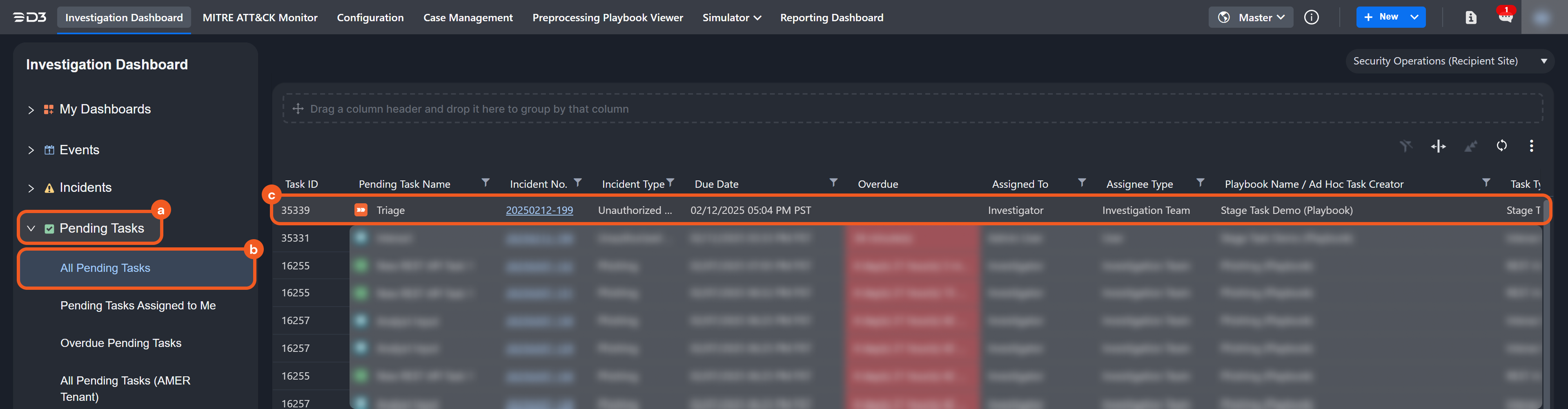
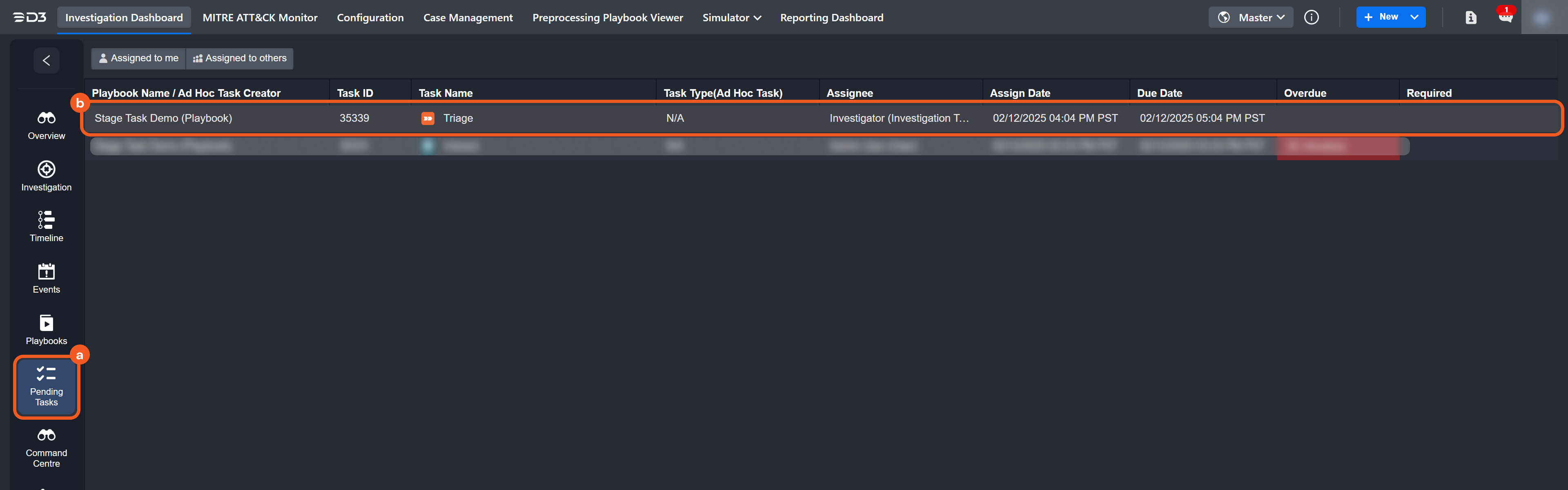
Stage Tasks as Pending Tasks
Investigation Dashboard
Incident Workspace
Example 1 - Kick-Starting an Investigation Unit
objective
Understanding the impact of assigning an assignee by role.
-
Ensure a Demo Investigator role is created and configured to be able to edit accessible records.
-20250311-021725.png?cb=e8d7c7980d7196a65bfd105d4b9edc8b)
-
Ensure that at least one user is assigned the Demo Investigator role.
-20250311-022018.png?cb=6dc8ec5a66da71b3ef59bec2c6bd5af8)
-
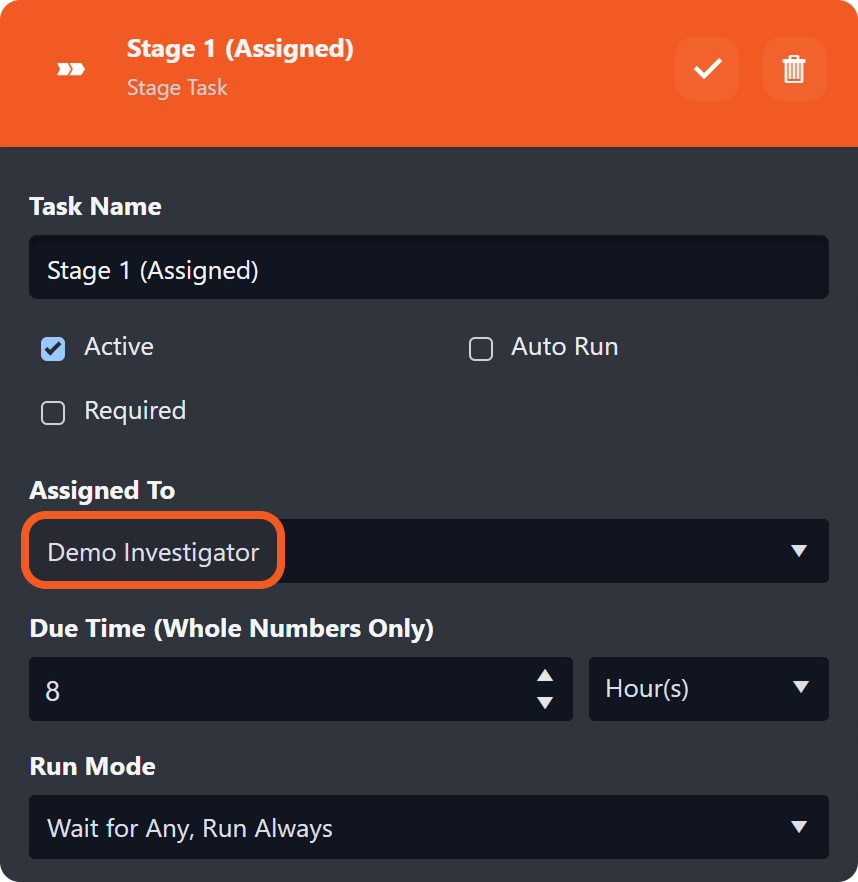
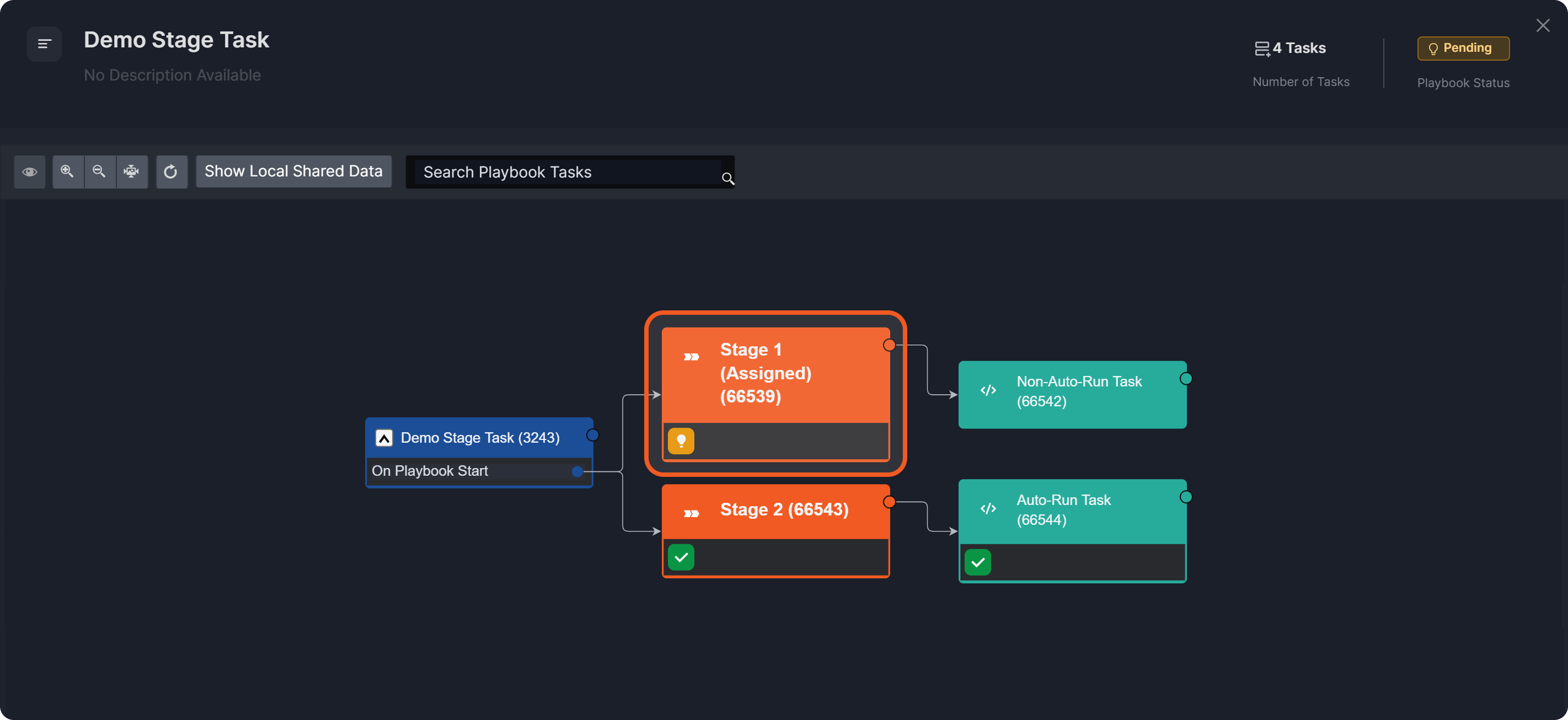
Create the following investigation playbook, assigning the Stage 1 (Assigned) task to users with the Demo Investigator role.
%201.png?cb=ee0a46e480399085d596d9530be59639)
READER NOTE *
-
Configure all tasks in the top execution stream to non-auto-run.
%201-20250303-220109.png?cb=ab9e9b3788edad90c6645669157c6180)
-
Configure all tasks in the bottom execution stream to auto-run.
%201-20250303-220055.png?cb=cab6e709edb58d0d15bb4e54ef659eef)
-
Submit this playbook.
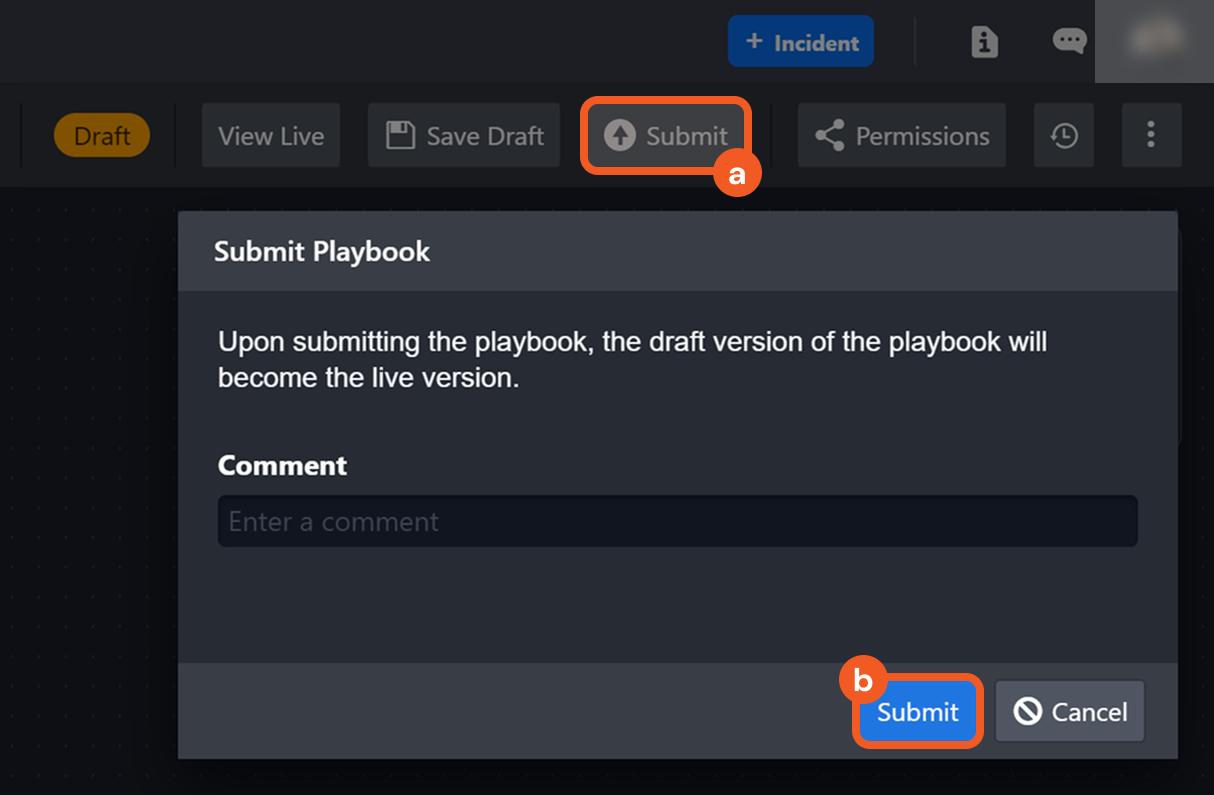
-
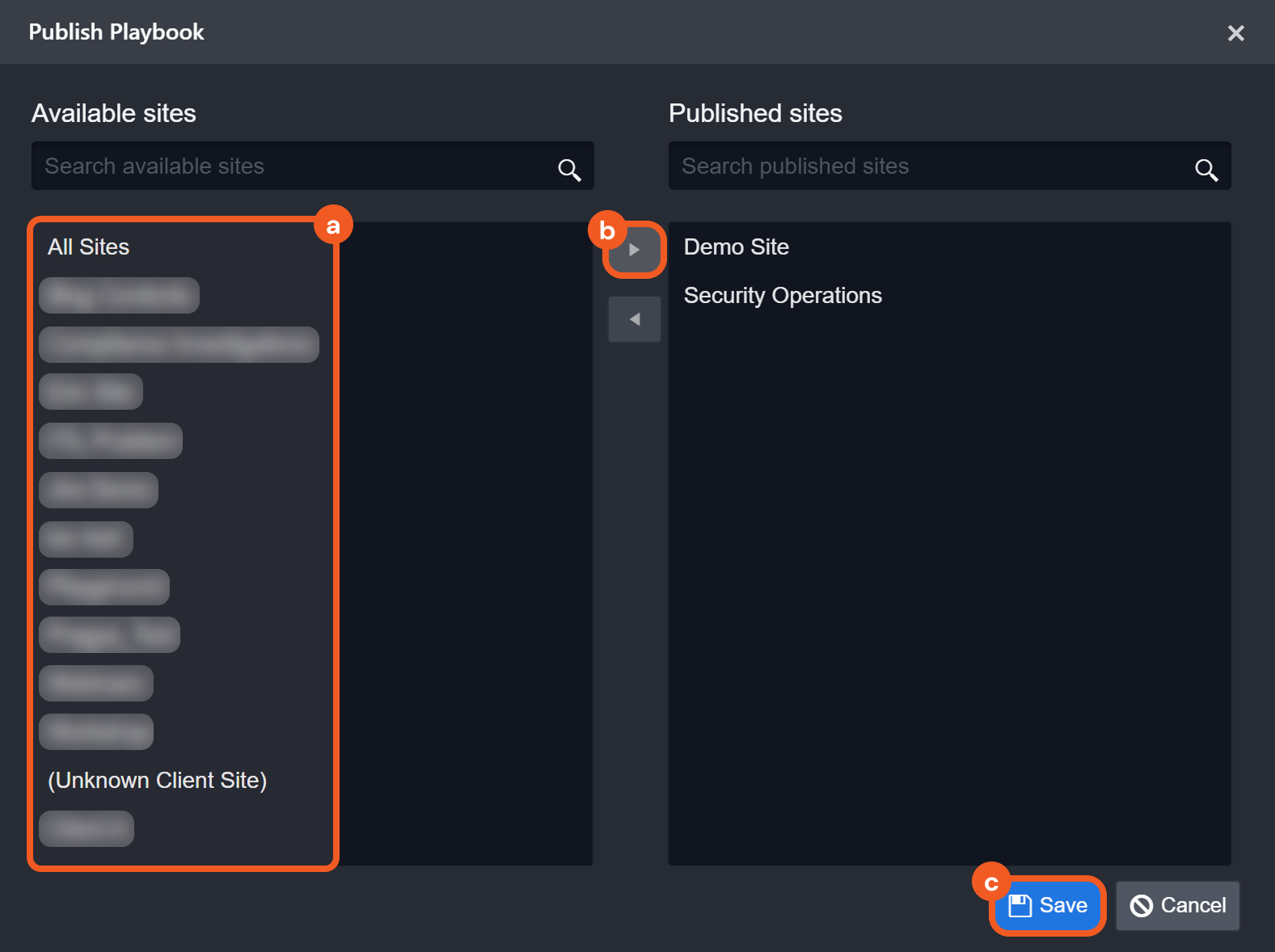
Publish this playbook to the relevant sites.
-
Click on the


-
Navigate to the Playbooks sub-module within the incident workspace.
-20250311-022605.png?cb=729049221cd7c7081004f37f9d980959)
-
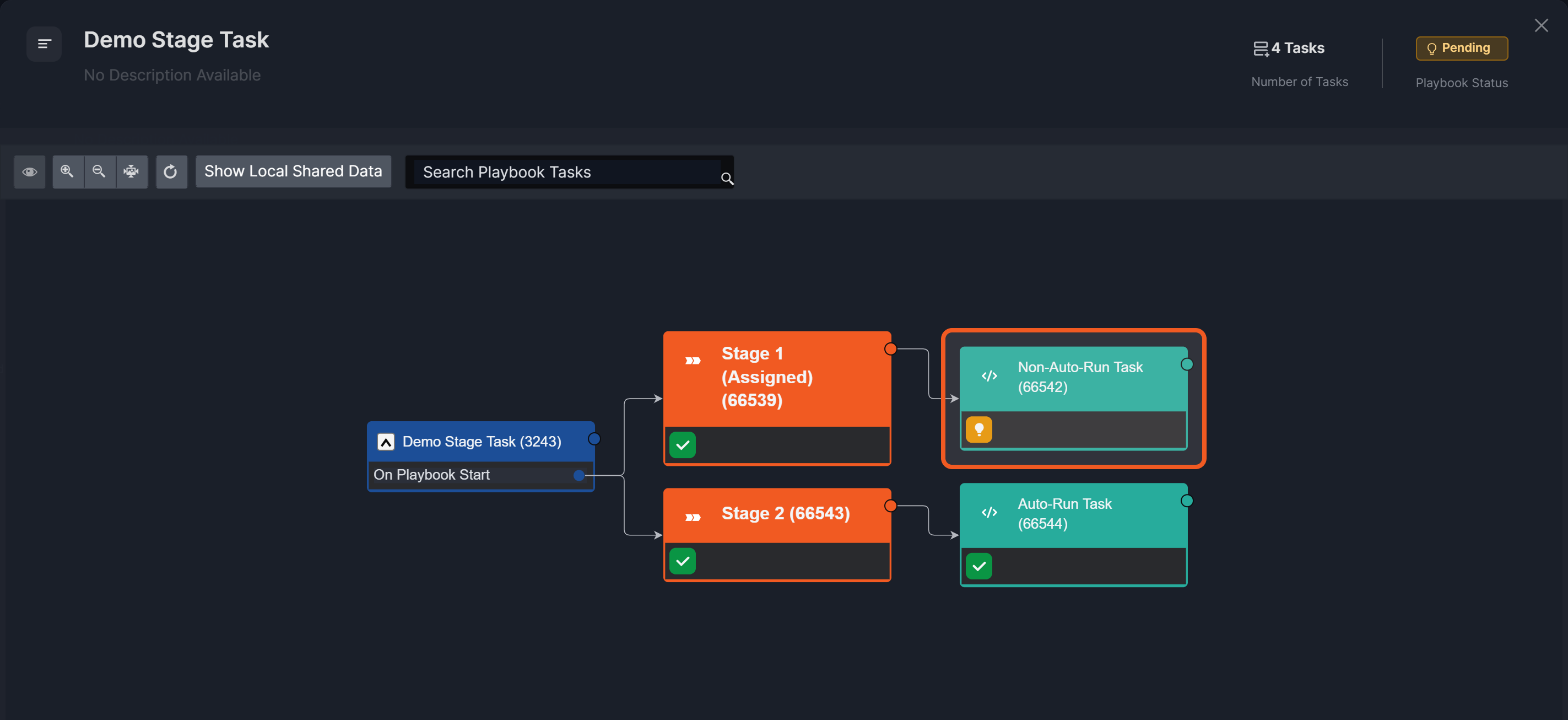
Click on the pending Stage 1 (Assigned) task.
-
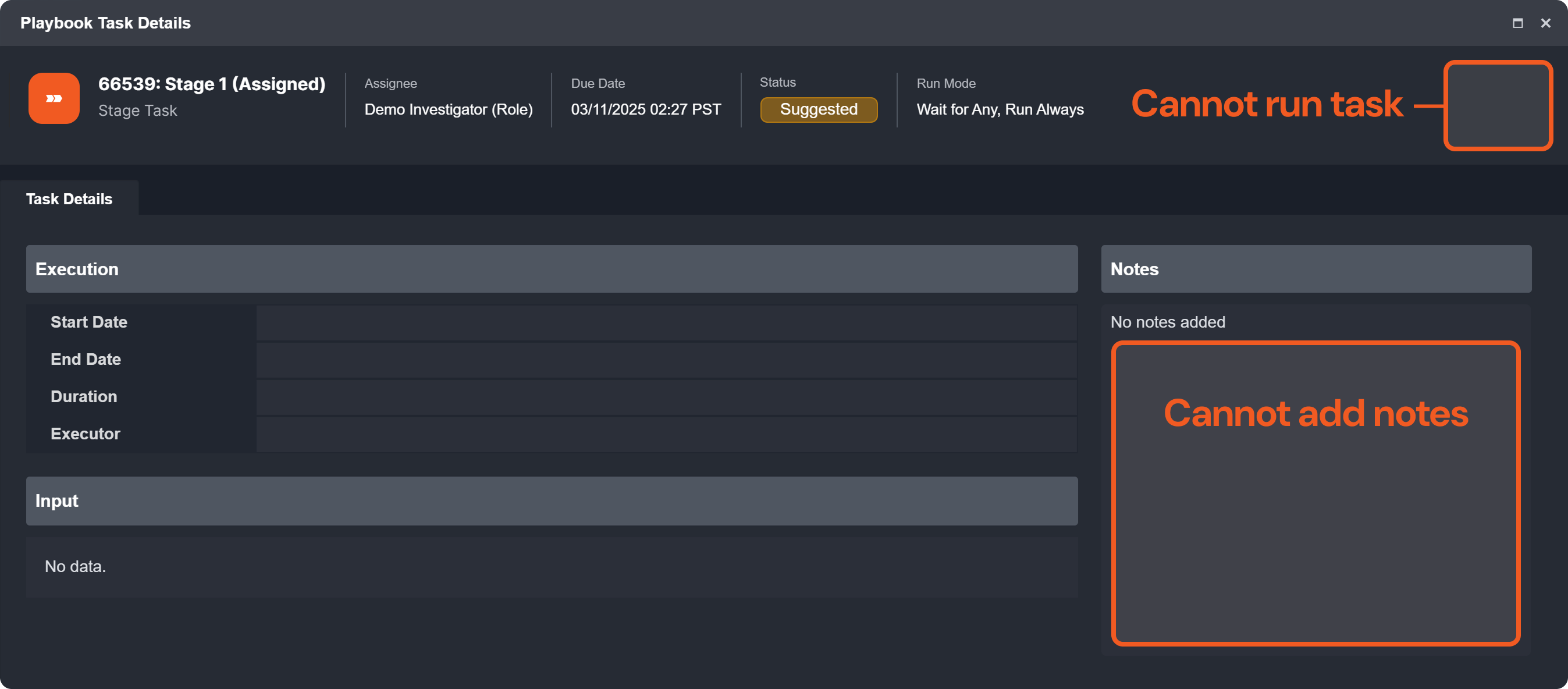
View Based on Assignment:
-
Assignees
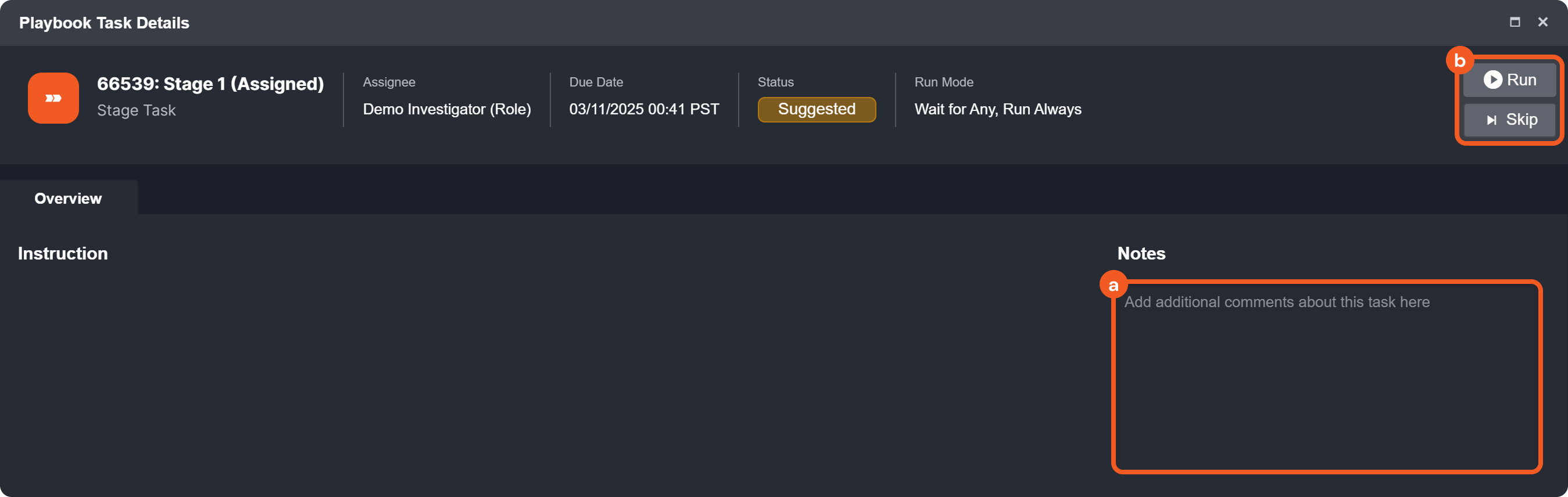
-
Non-Assignees (with the same role)
-
-
Assignees can now track workflow progress, monitor execution, provide required inputs, document outcomes, and take actions per SOC or business requirements.
Example 2 - Building and Testing a Playbook for IP Reputation Analysis
scenario An analyst is building a playbook to check IP reputation, using stage tasks to organize workflow and ensure an email is sent only after the preceding stage task executes.
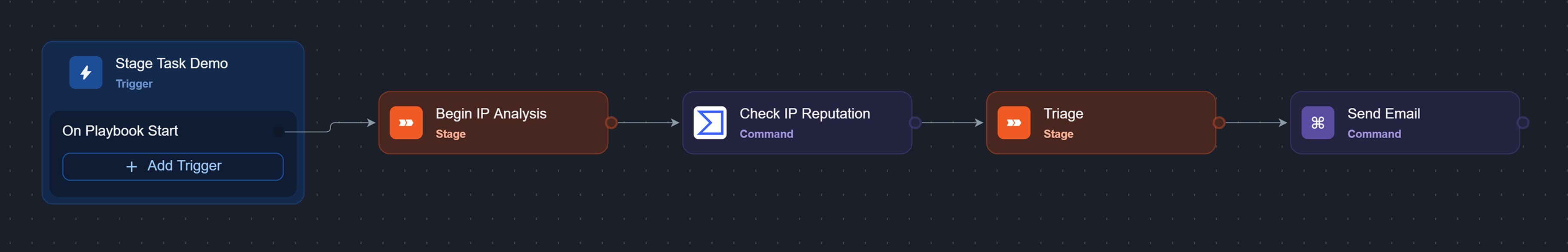
Here is how they built the playbook:
-
Add a stage task to the On Playbook Start trigger to mark the beginning of the IP analysis.
-
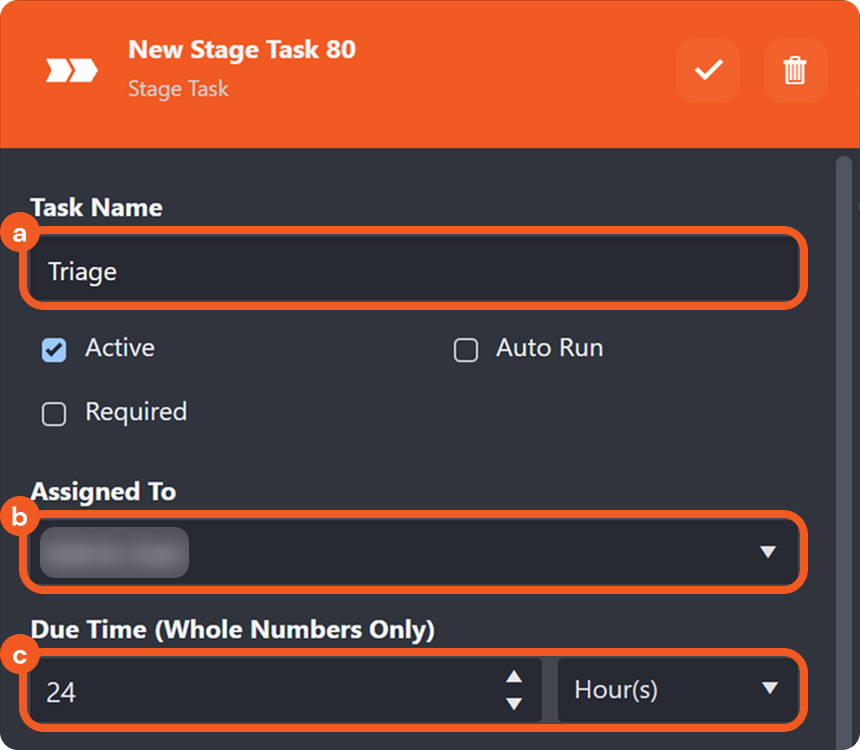
Name the task Begin IP Analysis, select the Auto Run checkbox, then click the Group 112.png button to save.
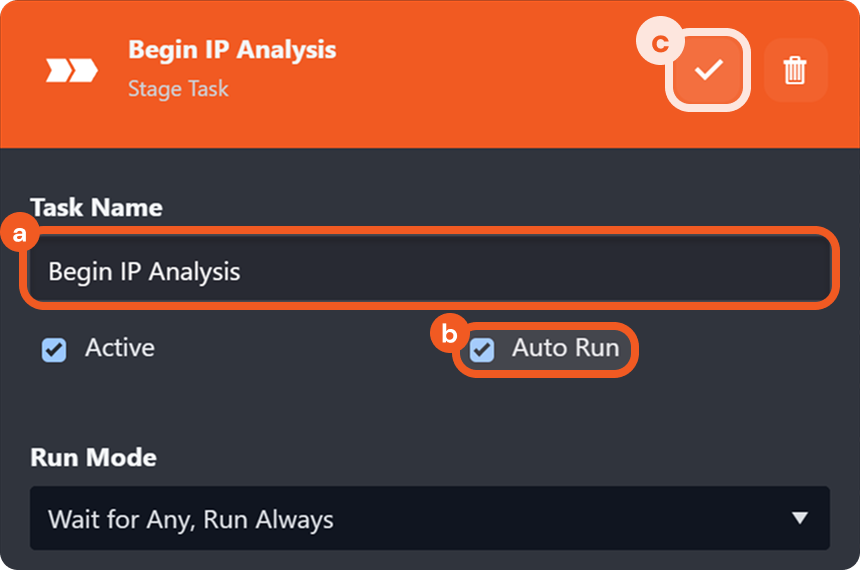
-
Add a command task that can check the reputation of IP addresses (e.g., the Check IP Reputation command from VirusTotal v3) to the stage task, and configure it.
-
Add a stage task to the previous task to control the workflow progression.
-
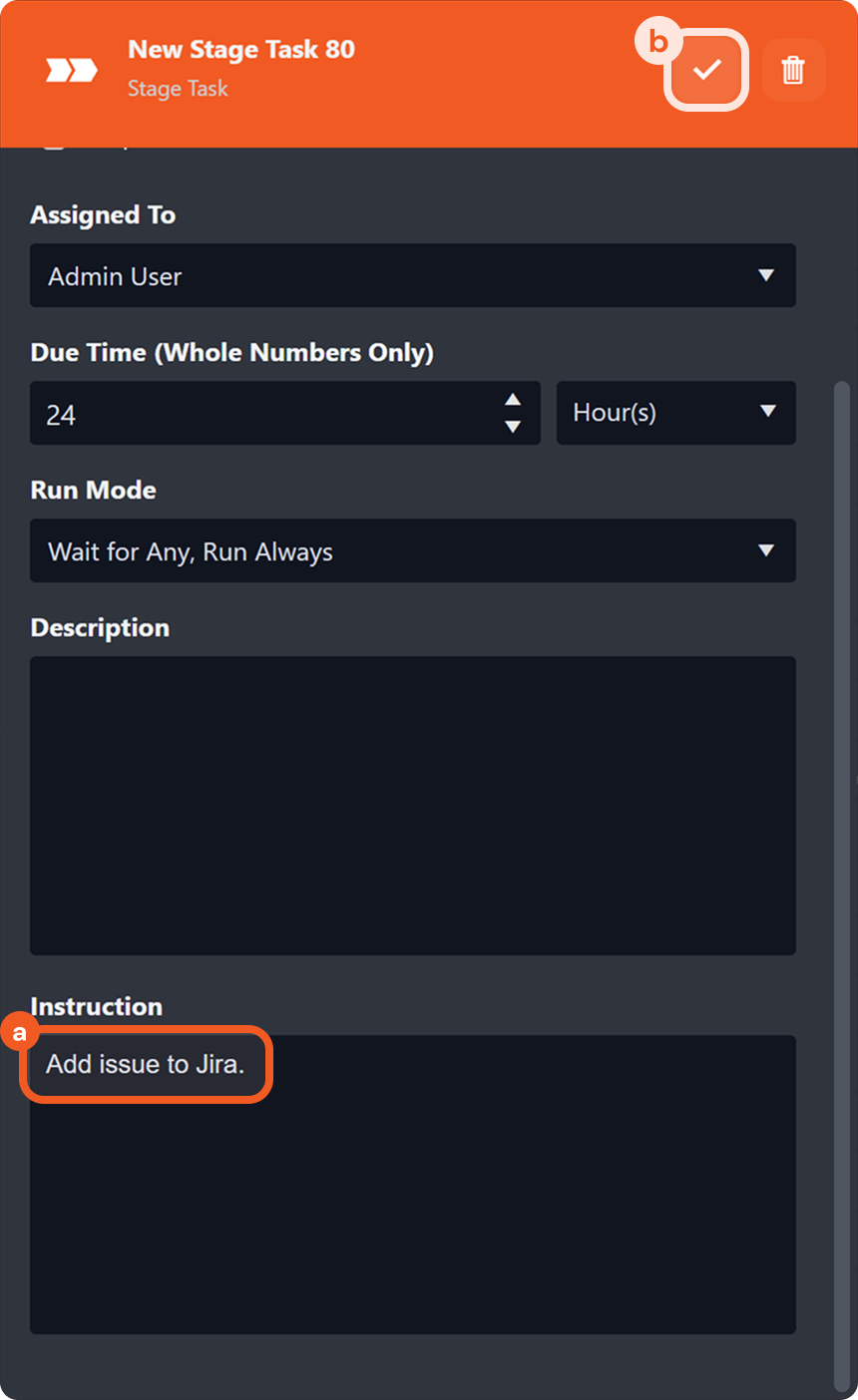
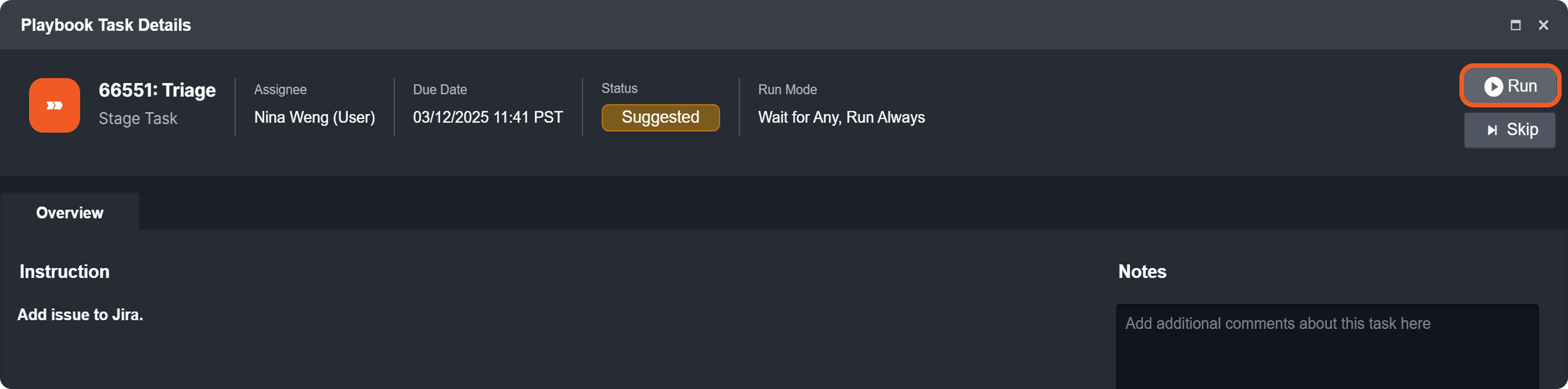
Name the task Triage, assign it to a user, and set a due time.
-
(Optional) Add an instruction for the assignee, then click the

-
Add the Send Email utility command task to the previous task, and configure it.
-
Submit this playbook.
-
Publish this playbook to the relevant sites.
-
Click on the Frame 29-20250311-020852.png button, configure the incident to run the submitted playbook, then click on the Frame 30-20250311-021142.png button.
-
Ask the assigned investigator to click the assigned stage task in the Pending Tasks Assigned to Me view on their investigation dashboard.
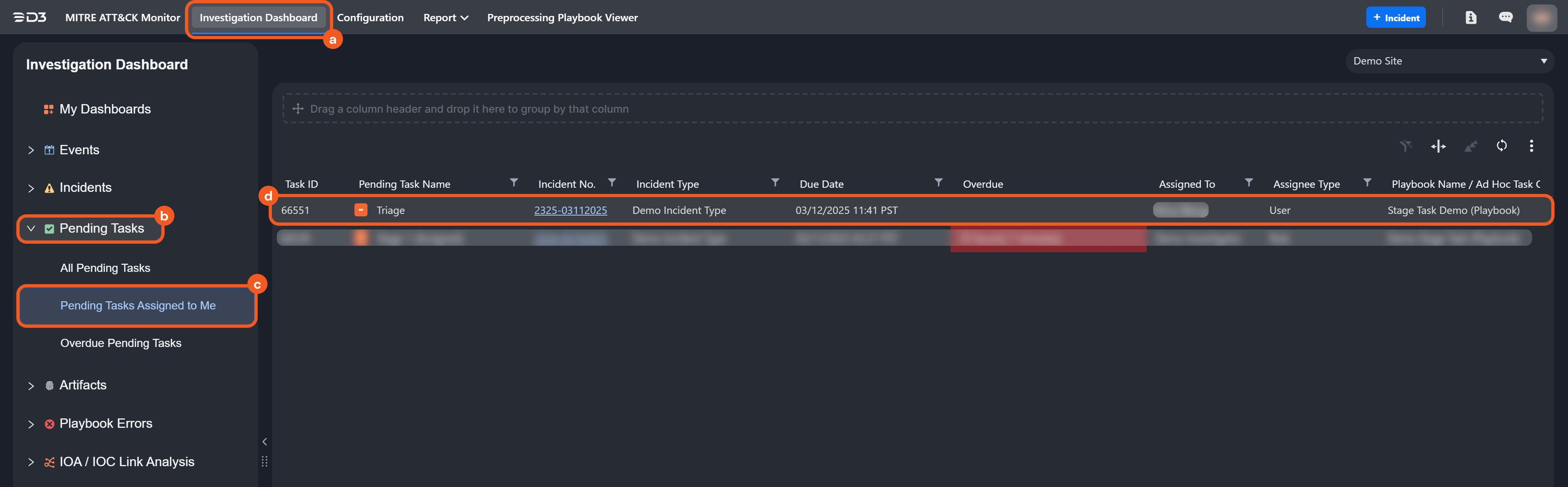
-
Ask the investigator to click the Run button after performing the task stated in the Instruction section to move along the playbook execution.
RESULT
Executing the Triage task enabled the subsequent Send Email task to run. The recipient will receive the email sent by the command task, as shown in the image below.